Protecting Idaho's information
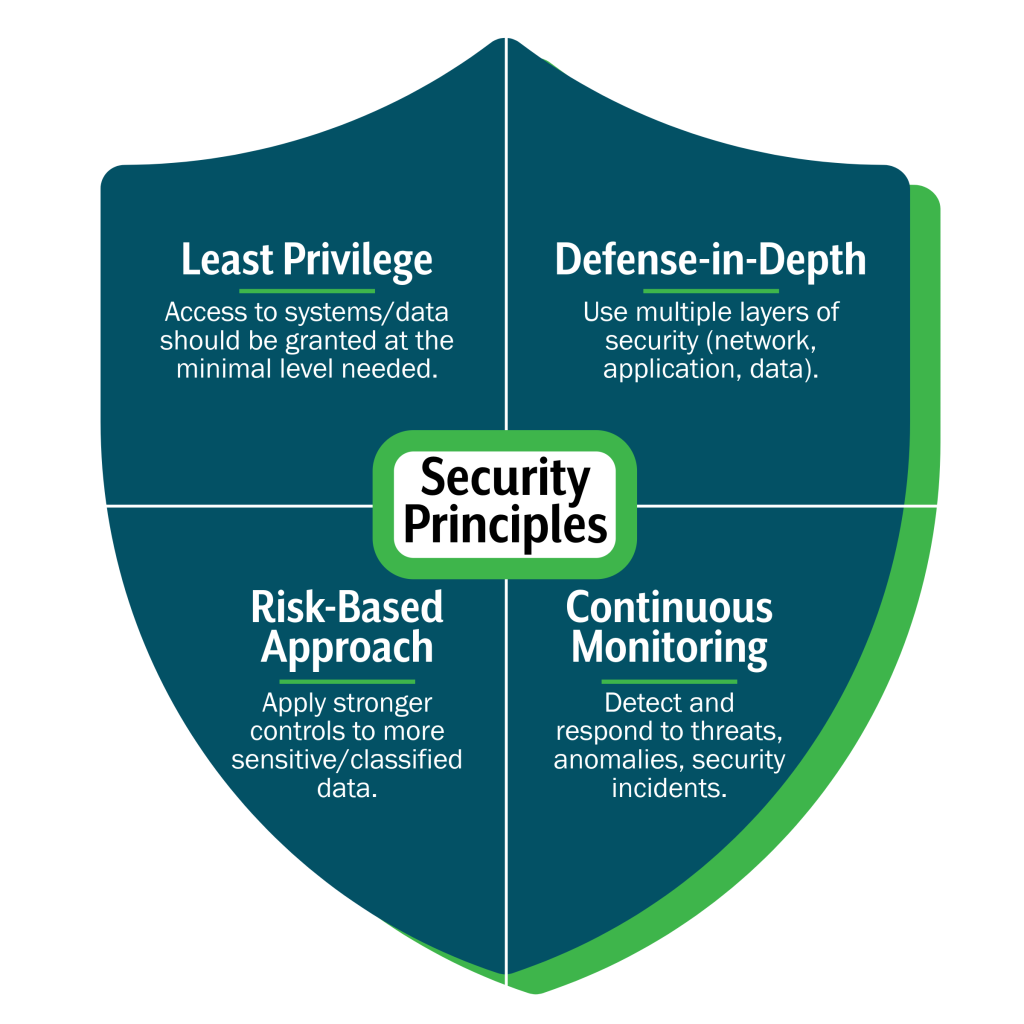
Data security is the practice of safeguarding information from unauthorized access, corruption, or loss. Data systems hold sensitive information that supports critical services, including public health, transportation, and citizen records. Protecting this data is essential to maintain public trust, comply with state and federal regulations, and ensure continuity of government operations. Strong security measures help prevent breaches and reduce risk.
Key security controls
Access Management
Managing who can access systems and data is the foundation of security.
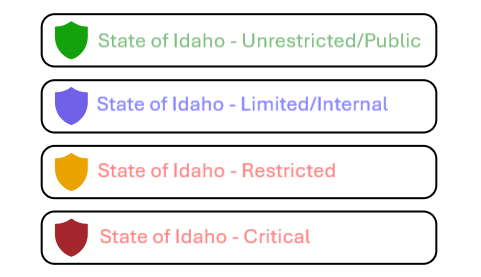
Using role-based access controls (RBAC) ensures employees only have the permissions they need to do their jobs. Employees can do their part by properly utilizing Microsoft Purview data sensitivity labels to accurately classify digital assets.
Multi-factor authentication (MFA) adds an extra layer of protection for sensitive systems, and regular access reviews help prevent unauthorized use.
Data Protection
Where encryption is critical
In rest
When data is stored in databases, servers, or backup systems.
In transit
When data is moving across networks, such as during file transfers or API calls.
Encryption
Encryption is one of the most important tools for keeping information safe. It works by converting readable data into a coded format that can only be unlocked with the right key.
This means that even if someone gains access to the data, they can’t understand or use it without authorization.
Key Management
Key management is just as important as encryption itself. Keys are what unlock encrypted data, so they must be handled carefully. Best practices include:
- Rotating keys regularly to reduce exposure
- Limiting who can access keys to authorized personnel only
- Storing keys securely using approved systems


Key Management
Key management is just as important as encryption itself. Keys are what unlock encrypted data, so they must be handled carefully. Best practices include:
- Rotating keys regularly to reduce exposure
- Limiting who can access keys to authorized personnel only
- Storing keys securely using approved systems
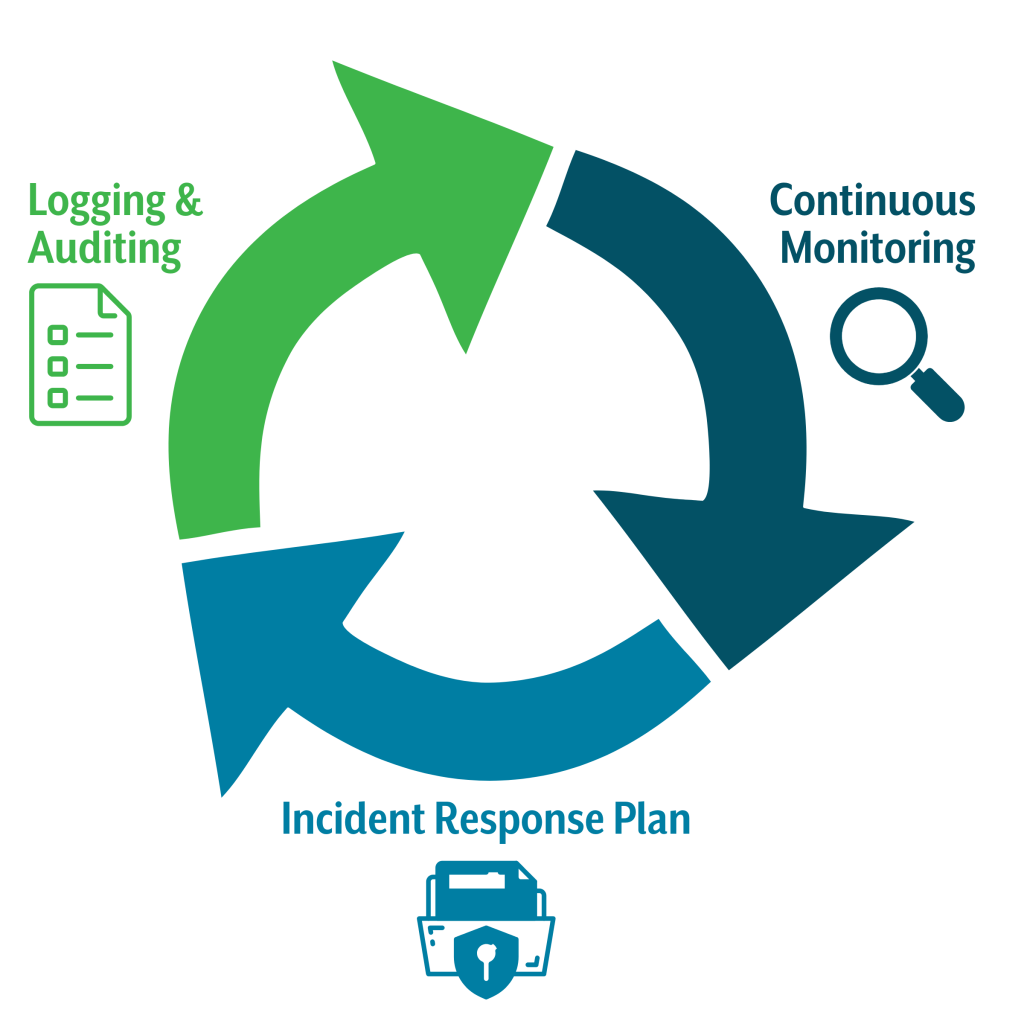
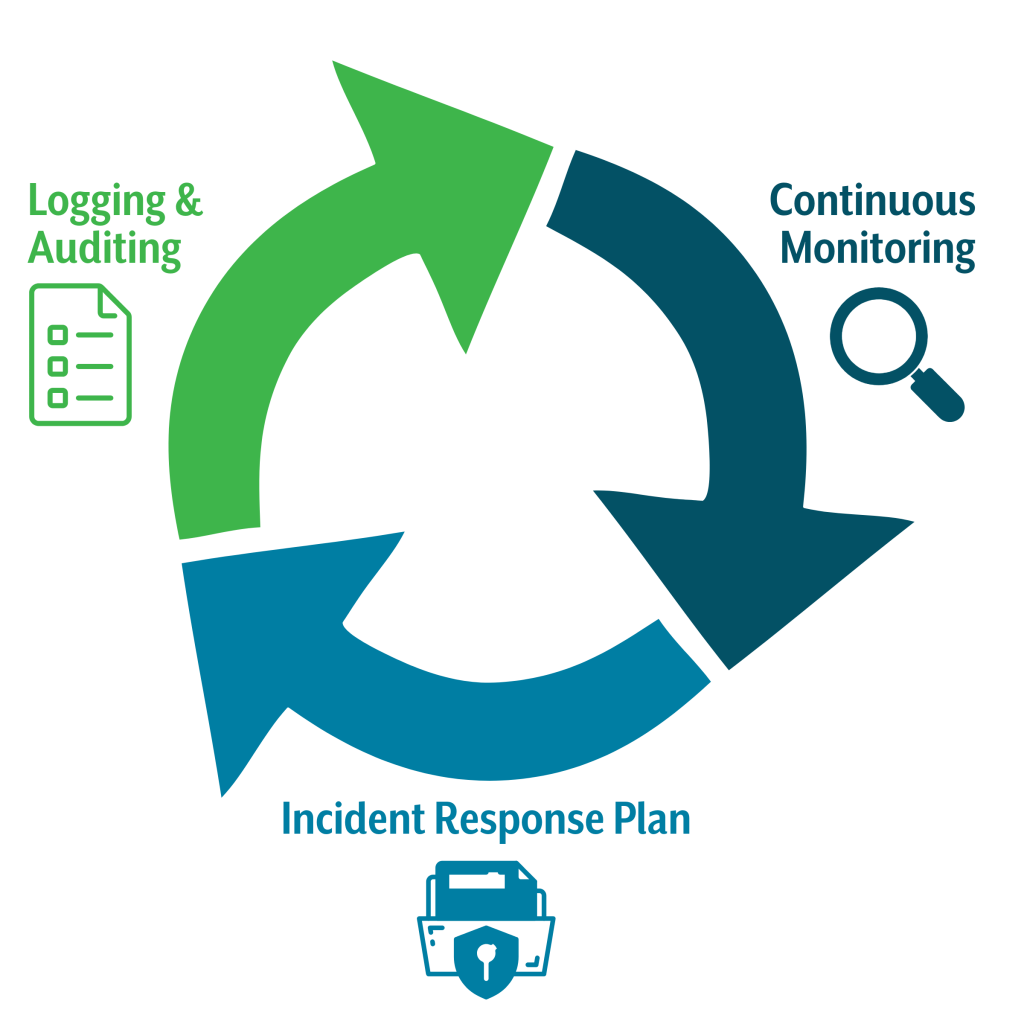
Monitoring & Incident Response
Security doesn’t stop at prevention, it requires vigilance and readiness.
Continuous monitoring and detailed logging help detect unusual activity before it becomes a major issue. When incidents occur, a clear response plan ensures quick action, minimizing impact and restoring normal operations.
Key practices
Logging and auditing: Record system access, changes, and failures.
Continuous monitoring: Use tools to detect anomalies in real time.
Incident response plan: Define clear steps and roles for handling security events, and practice with drills.
Key practices
Logging and auditing: Record system access, changes, and failures.
Continuous monitoring: Use tools to detect anomalies in real time.
Incident response plan: Define clear steps and roles for handling security events, and practice with drills.
Risk Management
A risk-based approach applies stronger controls to sensitive data.
Even with strong security, disruptions can happen. Some examples include cyberattacks, hardware failures, or natural disasters. Resilience means planning ahead so essential services continue and data remains safe. Idaho agencies implement business continuity and disaster recovery plans to keep services running during disruptions.
Core strategies:
Business continuity and disaster recovery (BC/DR): Regular backups and tested recovery procedures.
Risk-based approach: Apply stronger protections to sensitive or classified data.
Vendor risk management: Assess third-party security before sharing data or integrating systems.
