Responsible stewardship of data
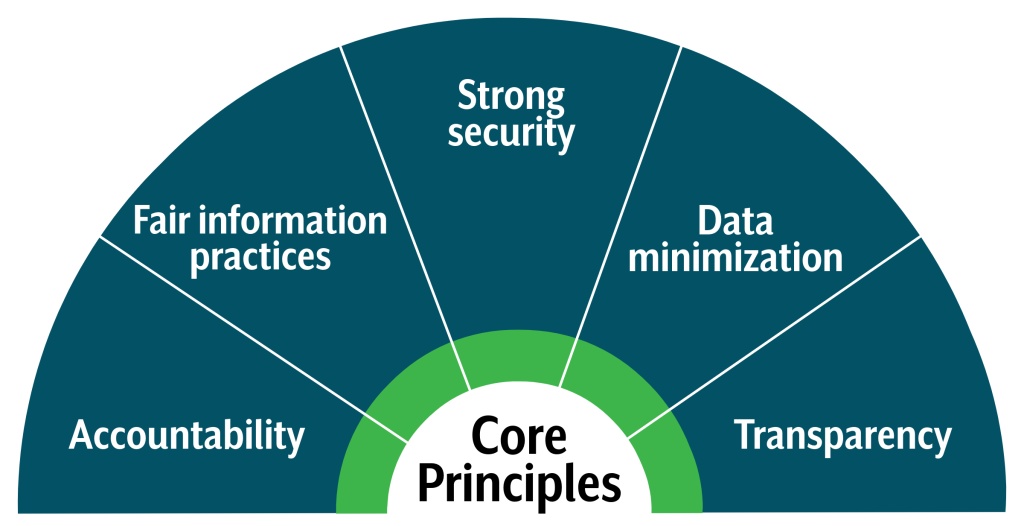
Data is a valuable public asset used to deliver effective services. At the same time, we recognize the responsibility to safeguard the privacy of the individuals we serve. Our approach to data privacy is grounded in five core principles →
These principles guide how we collect, use, share, and protect information across all state agencies, ensuring that public data is managed with integrity and respect.
Key privacy controls
Data Classification
Data classification helps employees understand how sensitive information is and what protections it requires. Correct classification reduces the risk of accidental exposure and ensures compliance with state and federal requirements.
Every dataset or document should be labeled according to its sensitivity—Public/Unrestricted, Internal/Limited, Restricted, or Critical.
These labels determine how the data must be stored, shared, accessed, and retained. Higher‑sensitivity data requires stronger safeguards, such as encryption and limited access.
Level 1
Unrestricted
Public data that includes information relating to the conduct or administration of a state agency and is typically created for public consumption.
Level 2
Limited
Internal data that includes sensitive information that may or may not be protected from public disclosure. Examples are audit reports or emails.
Level 3
Restricted
Confidential data that includes sensitive information intended for agency use only and is typically federally regulated. An example is medical records.
Level 4
Critical
Highly sensitive information where disclosure could cause significant harm, including potential injury, disability, or loss of life.

Guide to Data & Systems Classification
This guide outlines the Idaho Technology Authority’s data classification framework to ensure proper handling, labeling, and protection of information based on its sensitivity and potential impact if breached.
Use this guide when classifying data and/or systems.
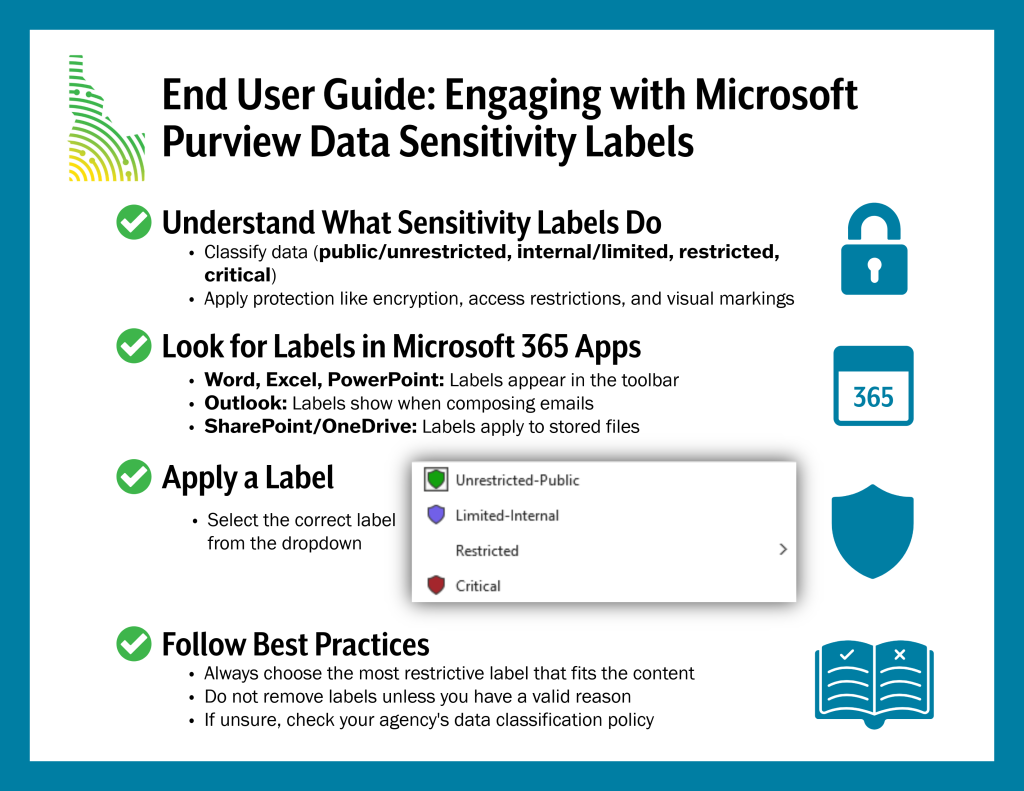
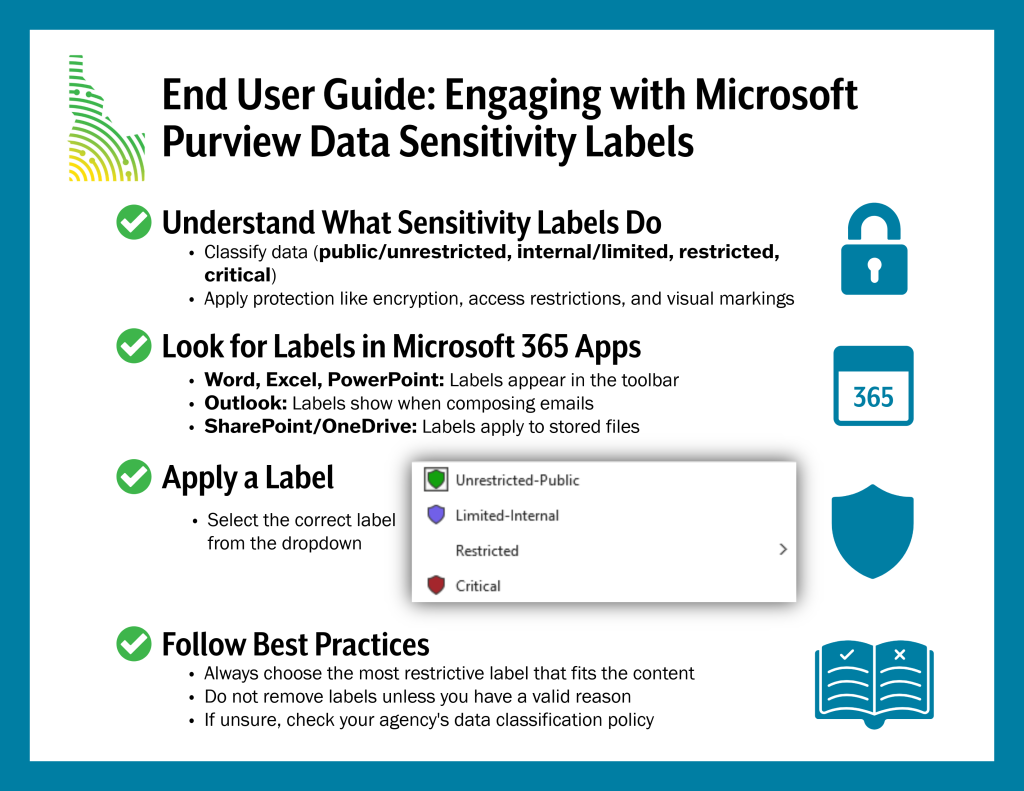
Microsoft Purview Data Sensitivity Labels
Microsoft Purview data sensitivity labels help classify and protect data based on its level of sensitivity. They allow agencies to apply consistent security and compliance policies, such as encryption, access restrictions, and visual markings across documents, emails, and other data assets. This ensures that sensitive information is handled appropriately and reduces the risk of accidental exposure.
Privacy Impact Assessment (PIA)
A Privacy Impact Assessment (PIA) is a structured review that identifies privacy risks before a new project goes live. Without it, sensitive information like names, emails, or financial details could be exposed through weak security or poor data handling practices. A PIA helps identify and address risks before they become problems.

When a PIA is required:
- Launching a new system or application
- Creating or acquiring a new dataset
- Implementing AI or automated decision‑making tools
- Making major changes to an existing system
What a PIA evaluates:
- Privacy risks and mitigation strategies
- Potential for re‑identifying individuals
- How data will be used, stored, shared, and retained
- Whether safeguards match the sensitivity of the data
Who approves a PIA:
A PIA is typically approved by the privacy officer, with input from compliance and information security teams. For high-risk projects, executive leadership may provide final sign-off.
Who maintains a PIA:
A data steward or privacy lead should keep the PIA updated and review it regularly, especially when the system or data changes.
Data privacy by design: Applying privacy to data flows
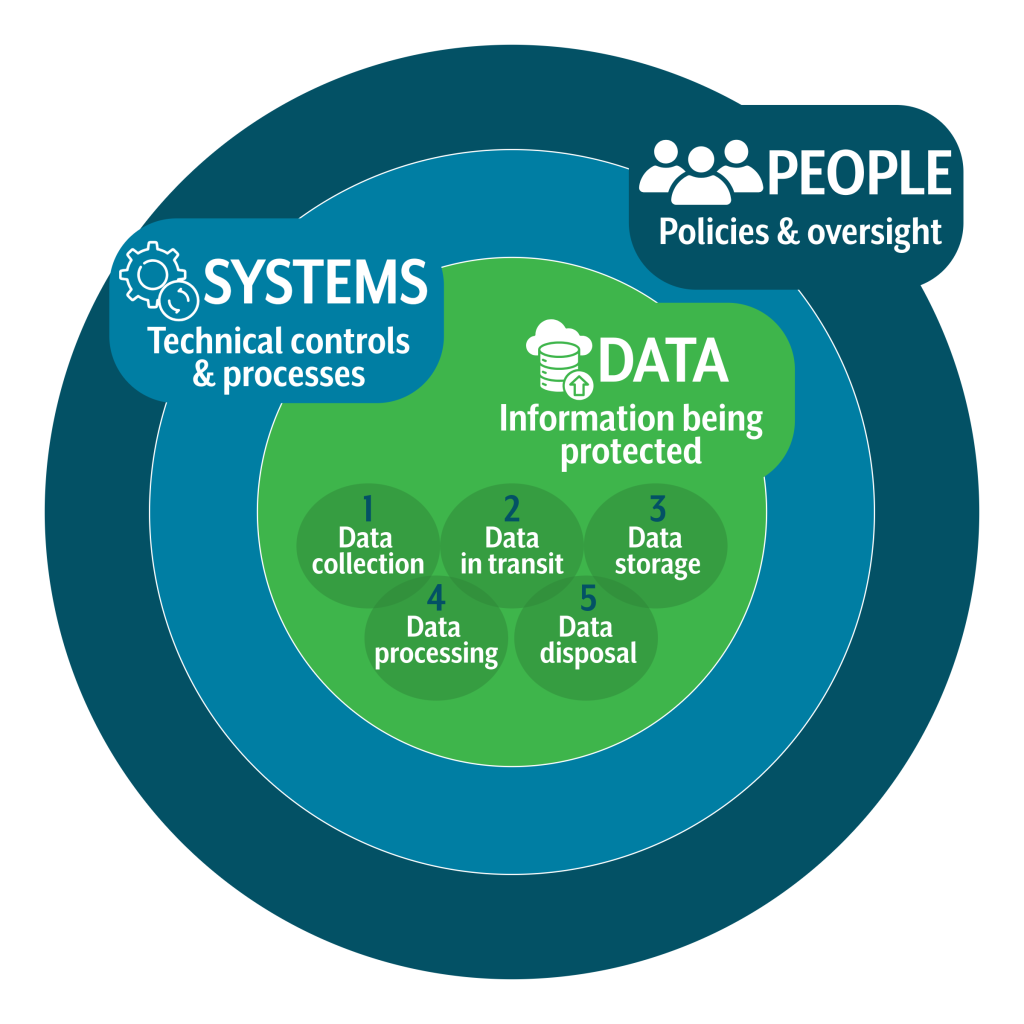
Privacy should be built into systems, processes, and technologies from the very beginning, rather than added later as an afterthought. This model portrays privacy by design as three interconnected layers: people enforce policies, systems enable secure processes, and data is protected at every stage.
Key privacy considerations
Data collection:
- The process of gathering information from individuals or systems. It is critical to ensure that only necessary data is collected and that users are informed about what is being gathered and why. Limiting collection reduces exposure to risk and supports compliance with data minimization principles.
Data in transit:
- Any information moving between systems, networks, or devices. This stage is vulnerable to interception and unauthorized access, making encryption and secure communication channels essential.
Data storage:
- How and where data is kept (databases, cloud, local devices). Proper storage practices, such as encryption and strict access controls, safeguard data against unauthorized access and tampering.
Data processing:
- The use of collected information for analysis, decision-making, or service delivery. It must align with user consent and legal frameworks to avoid misuse.
Data disposal:
- The secure deletion or destruction of information once it is no longer needed. This step prevents unauthorized recovery of sensitive data and supports compliance with retention policies.
Why it matters
Transparency & accountability:
- Users know how their data is handled, and organizations can demonstrate responsible practices.
Regulatory compliance:
- Avoid fines and legal consequences by adhering to laws like GDPR, CCPA, HIPAA.
Building trust:
- Customers and partners are more likely to engage with organizations that respect privacy.
Risk management:
- Reduces likelihood of breaches, financial loss, and reputational harm.
The Privacy Framework by the National Institute of Standards and Technology (NIST) focuses on enabling better privacy engineering practices that support privacy by design concepts.
Creating a Privacy Program: A Roadmap for States by NASCIO
NASCIO’s roadmap outlines 6 important phases of starting a privacy program from scratch:
- Establish foundations
- Develop governance
- Operationalize privacy
- Build awareness
- Incident management
- Monitor and improve
When collecting personal data, it’s essential to ensure that your practices comply with legal requirements and respect user rights.
Align with legal or statutory purposes
Only collect personal data for purposes that are lawful and clearly defined. This means having a valid legal basis, such as user consent, contractual necessity, or compliance with regulations—before processing any information.
Minimize data collection
Gather only the personal data that is strictly necessary for the intended purpose. Avoid collecting extra details “just in case,” as this increases privacy risks and may violate data protection laws.
Anonymize when possible
Whenever feasible, remove or mask identifiers so individuals cannot be easily linked to the data. Techniques like anonymization or pseudonymization help reduce the impact of potential breaches and strengthen privacy protections.
Managing personal data responsibly doesn’t end after collection, it includes knowing how long to keep it and how to securely dispose of it.
Define retention schedules
Based on data classification, create clear retention schedules that specify timeframes for each data category, ensuring compliance with regulations and reducing unnecessary storage.
Securely dispose of data
When data reaches the end of its retention period, dispose of it in a way that prevents recovery or misuse. This can include permanent deletion from systems, secure shredding of physical documents, or anonymizing data so individuals can no longer be identified.
Protecting sensitive data requires strict control over who can access it and continuous monitoring of that access.
Limit access based on roles and need
Only grant access to individuals who need the data to perform their job. Implement role-based access controls (RBAC) to ensure users can only view or modify the information necessary for their responsibilities.
Use authentication, authorization, and encryption
Strengthen security by requiring strong authentication (e.g., multi-factor authentication), enforcing proper authorization checks, and encrypting sensitive data both in transit and at rest. These measures help prevent unauthorized access and data breaches.
Maintain and review audit logs
Keep detailed logs of who accessed what data, when, and why. Regularly review these logs to detect unusual activity or potential misuse. Audit logging is essential for accountability, compliance, and incident response.