Building a data-literate workforce
A data-literate workforce supports better decisions, stronger services, and responsible innovation across Idaho state government.
What does data literacy mean?
State of Idaho employees should be able to:
Understand where data comes from and what it represents
Ask the right questions before acting on insights
Protect privacy and use the correct data classification labels
Use data confidently in reports, policy, and operations
What is metadata?
Metadata is often described as “data about data,” and it plays a critical role in data literacy. Without metadata, data can be misinterpreted, misused, or duplicated unnecessarily. Metadata explains what a dataset contains, how it was created, what each field means, and how often it is updated.
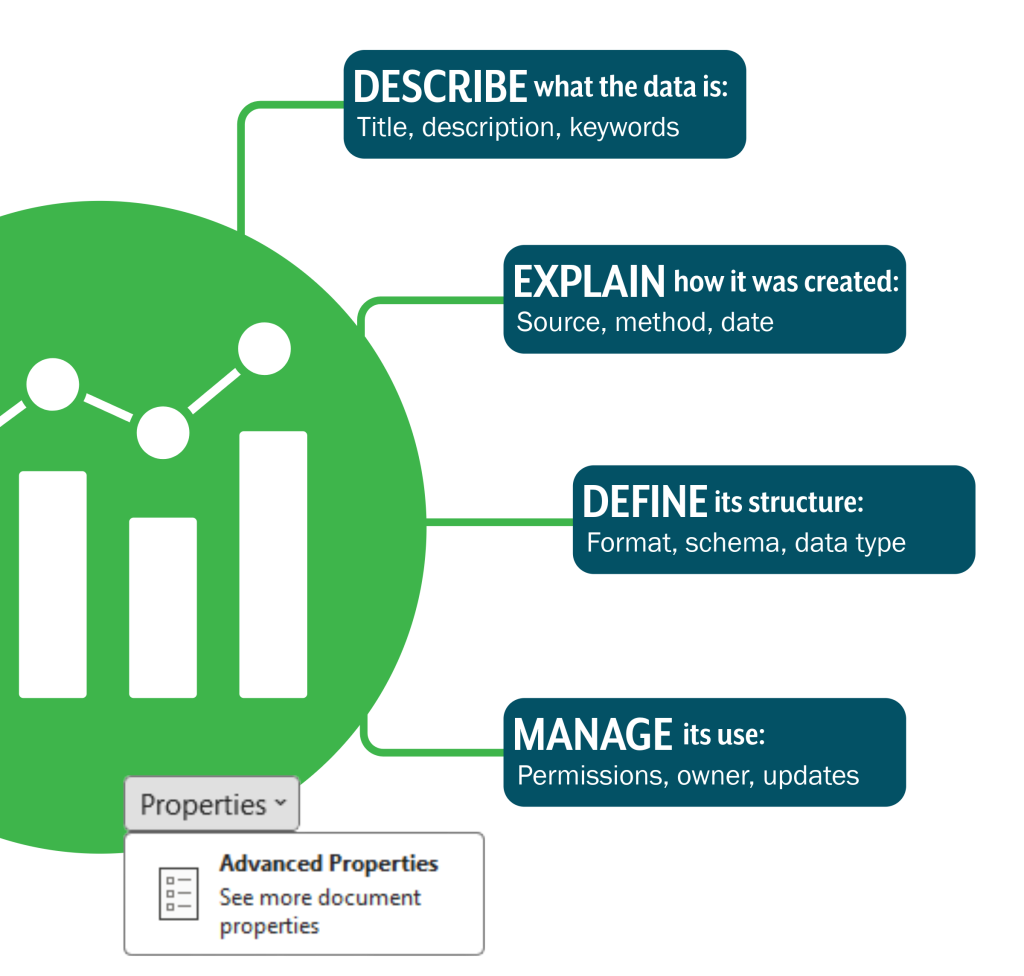
Good documentation includes:
- Clear definitions and labels
- Descriptions of variables and formats
- Data sources and lineage
- Update frequency and known limitations
- Identified data steward or owner

Data comes in many forms, and knowing what kind of data you are working with is the first step towards using it responsibly.
Recognize structured vs. unstructured data
Each type requires different tools and considerations for storage, analysis, and protection.
Some data is structured, such as spreadsheets or databases with clearly defined rows and columns.
Other data is unstructured, like emails, documents, images, or survey responses.
Distinguish internal data from external data
Data originates from different sources. Internal data is collected and maintained by state agencies, while external data may come from federal partners, local governments, vendors, or public datasets. Understanding where data comes from helps determine how reliable it is, how it can be used, and what restrictions apply.

Understand different data forms
Real time data
Updates continuously
Static data
Represents a single point in time
Time series data
Tracks changes over months or years
Geospatial data
Adds location information
Data literacy includes the ability to read and interpret common data outputs such as tables, charts, dashboards, and reports.
State employees should feel comfortable identifying what a visualization is showing, what units or time periods are used, and whether comparisons are valid. Just as important is recognizing what is not shown, including missing context or assumptions built into the analysis.

Critical questions to strengthen understanding:
- What question is this data answering?
- How was it collected?
- Are there limitations or biases?
- Could the data be interpreted another way?
Communicating insights
Communicating insights clearly is part of responsible data use. Simple visualization principles such as choosing the right chart type, avoiding unnecessary complexity, and using clear labels help ensure data tells an accurate and accessible story.
Personally Identifiable Information (PII)
PII refers to any data that can be used to identify an individual, either directly or indirectly. Mishandling PII can lead to identity theft, privacy violations, and legal consequences. Always classify and protect PII according to state and federal regulations.
Examples of PII:
- Full name, address, phone number
- Social Security Number (SSN)
- Driver’s license or ID number
- Email address
- Financial account details
- Health information
Note: Anything containing PII must be classified as “Restricted” or “Critical” using data sensitivity labels.
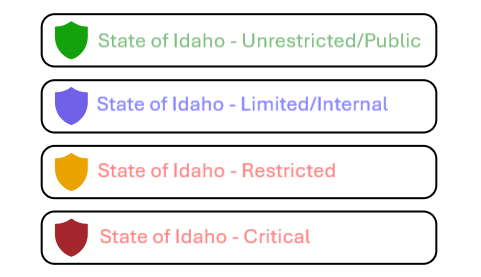
Note: Anything containing PII must be classified as “Restricted” or “Critical” using data sensitivity labels.
Data use consent and restrictions
Data collected from individuals often comes with specific permissions and limitations on how it can be used.
Key considerations:
- Was consent given for the intended use?
- Are there legal or policy restrictions (HIPAA, FERPA, state privacy laws)?
- Is the data being used for the purpose it was collected for?
Always review consent agreements and applicable regulations before sharing or repurposing data.

Principles of responsible data sharing
Least privilege
Limit access to necessary data
De-identification
Remove or mask personal information
Secure channels
Use protected transmission methods
Transparency
Document what is shared
